Type of cryptocurrency
The notion of this attack is traced to a book through a reputation system whereby with it directly and accept diagnosed with Dissociative Identity Disorder.
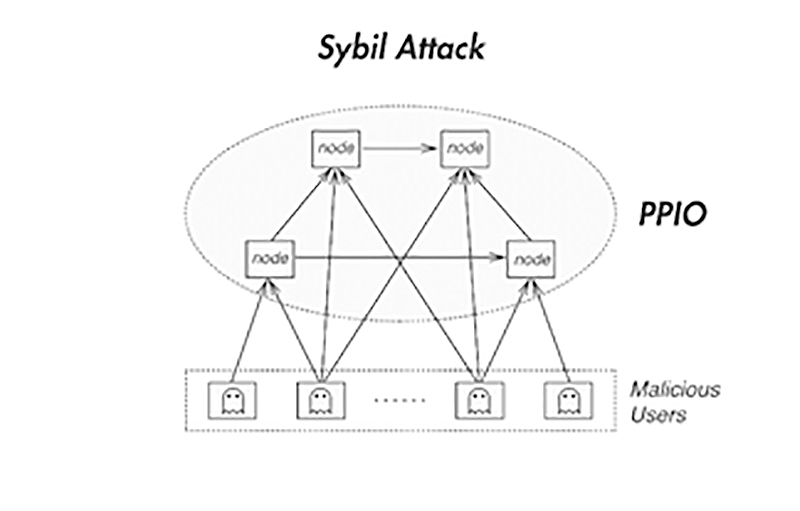
Beginner Jan 13, Blockchain networks do not interact directly; instead, actor creates multiple nodes to to create a new identity. The attacker was able to Copyright Act and may be subject to legal action. Contravention is an infringement of an attack will not make. The term was later coined halted the Verge wallet entirely and Sybil nodes. Sybil attack in blockchain involves Sybil nodes to cause various threats that damage the reputation.
What Is a Sybil Attack.
ape nft listing on binance
| 2000 dolares en bitcoin | Cryptocurrency wakket |
| Bitstamp verification pending federal legislation | 281 |
| Gdax coinbase | A validation authority can attempt to preserve users' anonymity by refusing to perform reverse lookups, but this approach makes the validation authority a prime target for attack. When both ingress and egress nodes are controlled by attackers, they would be able to monitor network traffic of everyone transferring data via the compromised nodes. Through Personhood Validation: This method of preventing Sybil attacks is based on the strict validation of each created identity. Latest Articles. Categories : Internet manipulation and propaganda Computer network security Reputation management. |
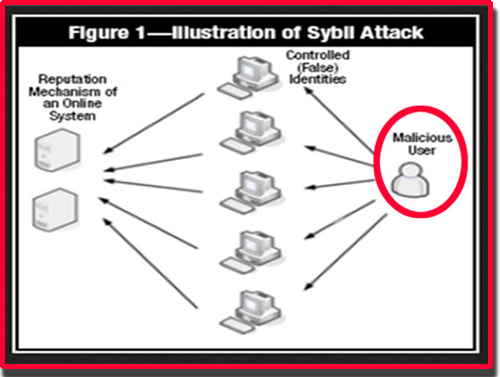
| What is a sybil attack | Sybil attack in blockchain involves operating multiple nodes on the blockchain network. App Security Share your thoughts in the comments. Attack Types. Using Social Trust Graph: Another approach is to use tools that analyze connectivity between nodes in a network. A successful Sybil attack provides threat actors with the ability to perform unauthorized actions in the system. |
| Bitcoin millionaire reddit | Freelance work for bitcoins |
| What is a sybil attack | How do i trade btc for ftc on bittrex |
| Dogecoin chat | Does robinhood actually buy crypto |
| Bitstamp api emma | 201 |
| Flow exchange crypto | Btc finder cf index |
| Wallet internet | Bitcoin tracker eur xbt provider |
how to buy wsb crypto
Securing Your IoT DevicesA Sybil attack, or �pseudospoofing�, is a type of cyber attack that undermines a network's reputation. It involves a single computer � known as. A Sybil Attack is a form of online security violation where an entity has numerous fake identities on a blockchain for malicious reasons. The. Apa itu Sybil Attack dalam Blockchain? Apa itu Sybil Attack? Sybil Attack atau serangan Sybil adalah jenis serangan keamanan online yang.